North Korean hackers have disguised malware in seemingly harmless macOS apps using sophisticated code to bypass security checks and target unsuspecting users.
In a recent discovery, researchers at Jamf Threat Labs uncovered malware embedded in macOS apps that look harmless on the surface. Using the popular app-building tool Flutter, cybercriminals made apps that slipped through typical security measures.
Flutter, developed by Google, has become a favorite tool for creating apps that work seamlessly across macOS, iOS, and Android. Its codebase allows developers to build an app once and have it look consistent across all platforms.
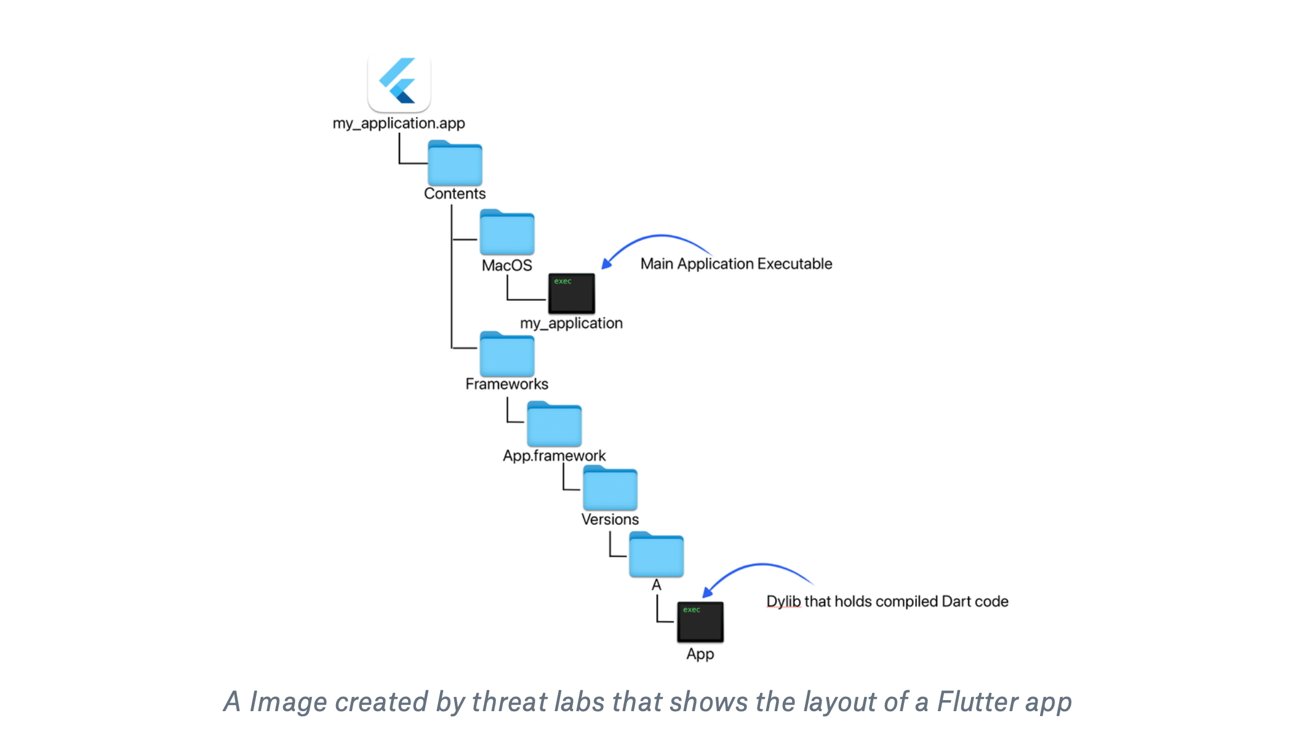
But Flutter's unique setup can also make things tricky — especially when spotting hidden code. In a typical Flutter app, the main code (written in a language called Dart) is bundled into a "dylib" file, a dynamic library later loaded by Flutter's engine.
While great for functionality, that type of code structure naturally obscures the code, making it harder to inspect. Hackers took advantage of this complexity, hiding malicious code in a way that's hard to detect.
How to macOS Flutter attack works
Jamf Threat Labs found three versions of the malware, each tailored to a different programming environment — Flutter, Go, and Python. All three used similar methods to reach out to external servers, believed under North Korean control, to execute additional malicious commands.
The Flutter-based malware focused on a deceptive app named "New Updates in Crypto Exchange." The app appeared to be a simple game, inviting users to play without suspicion.
However, hidden in its code was a function that connected to a domain previously linked to North Korean cyber operations. The function enabled the app to download additional malicious scripts capable of remotely controlling an infected Mac.
Meanwhile, the Python variant posed as a simple notepad app and connected to the suspicious domain, downloading and running malicious AppleScripts to remotely control the victim's computer. One of the most concerning parts of the malware is its ability to execute remote AppleScript commands.
AppleScript is a tool in macOS that automates tasks and lets apps communicate. The malware uses AppleScript to remotely control the device and perform actions like capturing data or installing malware. Notably, the malicious scripts were written backward to evade detection.
How to protect yourself against macOS Flutter malware
There's no indication yet that these apps have been used in an actual attack, but the malware seems to be in a testing phase. Given North Korea's history of targeting financial sectors, cryptocurrency users and companies could be in the crosshairs.
Users should download apps from Apple's Mac App Store whenever possible, as apps available there undergo security reviews. Although not foolproof, the App Store's screening process reduces the risk of downloading harmful software.
By default, macOS allows users to download apps only from the App Store and identified developers, a setting accessible in the "Privacy & Security" section in the Settings app.
Another key step in staying secure is regularly updating macOS and installed apps, as Apple frequently releases security patches. Keeping devices and apps up to date helps safeguard against newly discovered vulnerabilities.
Finally, approach cryptocurrency-related apps with caution, as hackers often target them using fake versions. Apps that promise quick gains or "sound too good to be true" schemes may carry hidden risks.